Email Phishing - Types, How to Detect & Avoid Attacks
We live in an era of clogged email inboxes. Spamlaws estimates that up to 45% of all emails are spam while other estimates are as high as 73%. Because of email’s widespread usage, it has become an extremely common entry-point for scams and cyberattacks. Unfortunately, we’ve all become used to solicited emails, making email-based cyberattacks a favorite tactic for fraudsters.
Why should you care about Email Phishing?
Email phishing is one of the greatest threats that businesses face today. dataprot.net provides the following key phishing statistics:
- Nearly one-third of all data breaches in 2018 involved phishing.
- A new phishing site is created on the internet every 20 seconds.
- More than 70% of phishing emails are opened by their targets.
- 90% of security breaches in companies are a result of phishing attacks.
- Small and mid-size businesses lose an average of $1.6 million recovering from a phishing attack.
- Apple is the most frequently impersonated brand by cybercriminals.
- More than 77% of organizations do not have a cybersecurity incident response plan.
All these stats show the relevance of phishing. Imagine a single neglectful click that may jeopardize your entire business. Thus, preparing your organization and employees to defend against email phishing is the need of the hour. This blog has all the details you need to protect your team against email-based phishing attacks.
What is Email Phishing?
According to NIST, phishing refers to "A technique for attempting to acquire sensitive data, such as bank account numbers, through a fraudulent solicitation in email or on a website, in which the perpetrator masquerades as a legitimate business or reputable person." Email phishing attacks occur when attackers, pretending to be some legitimate authority, send fake emails to users with the intention of tricking them into revealing sensitive data.
The most common end goal of phishing attacks is to steal financial information or network credentials. In many instances, email phishing can be the first step of larger multi-vector attacks which affect your entire organization. Attackers aim to enter organizational networks to plant ransomware or spyware, or gain unauthorized access to business-critical information, via employee emails. Get to know more about WannaCry - one of the most famous ransomware attacks in recent years.
Email phishing is a social engineering tactic. These types of cyberattacks manipulate human emotions and prey on feelings of fear, anxiety, or urgency. These emotions inhibit our critical thinking and lead to rash actions. The attackers want us to act as they say without thinking things through.
What are common Email Phishing Techniques?
There are three main techniques used to steal your sensitive data. These are:
- Malicious links
- Infected attachments
- Fake data entry forms
Let's elaborate on each of them next.
1. Malicious Links
Web links, or URLs, are generally part of most emails. In phishing emails, web links are the driver behind the scam. It’s pretty simple to create URLs that will infect your system with ransomware, virus, trojan, or other malware and compromise the entire network. Attackers can also create links that lead you to harmful websites or be hidden in seemingly safe download buttons.
2. Infected Attachments
Email attachments are often used to launch cyberattacks and cripple IT networks. Infected attachments can look like standard word documents, PDFs, or other e-files. Downloading a fake email attachment can destroy sensitive data or even allow the attacker to take control of your computer and other systems in your IT network.
Anti-virus solutions use signature-based detection to block malware automatically. To bypass this, attackers conceal an exploit inside the attachment. An exploit corresponds to a piece of software that takes advantage - in other words, it exploits - a bug or vulnerability to cause unintended or unanticipated behavior to occur on computer software, hardware, or other computerized electronics. When the attachment is downloaded, the exploit uses existing system vulnerabilities to download the indented malware into the system.
Another method/approach attackers use files with an embedded malicious macro. Fraudulent pop-ups ensure the user clicks on the “Enable Content” button that runs the macro and infects the underlying computer.
3. Fake Data Entry Forms
In this tactic/technique, attackers trick the victim into filling in critical information into fraudulent data entry forms. The information demanded can be user IDs, financial data, social security numbers, or phone numbers. For this tactic to work, attackers pose as legitimate figures from established companies, banks, or the government.
What are the known Types of Email Phishing Attacks?
Email phishing is the most general type of email-based scam meant to trick users into revealing their private information or downloading malicious content. In most cases, email phishing attacks are sent to a large number of people at once. The attackers spread a wide web without targeting anyone in particular. This type of attack assumes that the many recipients there are at least some that will fall for the trap.
Other types of email-based phishing attacks are more targeted in nature. These are:
- Spear Phishing
- Whaling (CEO Fraud)
- Business Email Compromise (BEC)
- Clone Phishing
Next, we will explore each of the four attack types.
Spear Phishing
Spear phishing, derived from the fishing technique where spears are used to target specific fish, is precisely what its name implies. Spear phishing is the opposite of randomized general phishing as it targets specific people. Usually, the targets are higher on the management chain with valuable information and privileged access. This kind of phishing requires the attacker to have special knowledge of the target organization’s structure and personnel.
Whaling (CEO Fraud)
Whaling, also called CEO fraud, happens when attackers pose as the CEO of a company and send the company’s executives an urgent email requiring instant action. A usual tactic is to trick employees into believing the CEO is asking for an urgent money transfer.
Business Email Compromise (BEC)
These phishing attacks target specific companies to defraud them and their partners, vendors, and clients. A common BEC tactic is to clone the business’s email or hack an employee’s email account and use it to request payment from vendors with fake invoices.
Clone Phishing
This is an advanced form of phishing where attackers use previously sent legitimate emails with links or attachments. Attackers clone legitimate emails and create a perfect copy where the links or attachments are replaced with malware. The phishing email appears as a simple re-send of the original email. This is a dangerous tactic because spoofed emails are hard to identify.
How to detect a Phishing Email?
Many times it’s impossible to differentiate a fake email from a legitimate one if phishing attacks are very cleverly carried out. Nevertheless, there are some common signs you should look out for when opening an email. Here are some red flags:
- The email starts with a general greeting, like “Dear Customer.” Legitimate companies will know your name.
- The email has grammatical errors. Companies sending emails to their clients make sure there aren’t grammar or spelling errors in their text. Read the email carefully to see if any writing error stands out – it could be a sign that something’s wrong.
- Legitimate companies, banks, or government agencies don’t ask for private information over email via a link or an attachment. If you get such unsolicited emails, there is a high chance it’s a scam.
- If the company domain name or logo seems unusual, it’s a glaring sign of a phishing email. Alternations of domain names, like added numbers or random letters at the end of the email address, can indicate a fake email.
- Legitimate email links match the destination address. The link text should be identical to the displayed URL when you hover your cursor over the link.
- Another simple way to identify a potential phishing attack is to look for discrepancies in email addresses. For example, it is worth checking against previous correspondence that originating email addresses match.
-
Check out for suspicious attachments. If an email with an attached file is received from an unfamiliar source, or if the recipient did not request or expect to receive a file from the sender of the email, the attachment should be opened with caution. If the attached file has an extension commonly associated with malware downloads (.zip, .exe, .scr, etc.) – or has an unfamiliar extension – recipients should flag the file to be virus-scanned before opening.
-
Determine whether the email contains threats or poses or urges for urgent actions. Emails that threaten negative consequences should always be treated with suspicion. Another tactic is to use a sense of urgency to encourage, or even demand, immediate action in a bid to fluster the receiver. The scammer hopes that by reading the email in haste, the content might not be examined thoroughly so other inconsistencies associated with a phishing campaign may pass undetected.
While these are common indicators of phishing attempts, they’re not fool-proof detection guidelines. Attackers have become highly advanced and knowledgeable. Even if you receive an email without any red flags, be careful before responding. Check out OpenDNS's phishing quiz to test how good you are at telling the difference between a legitimate website and one that's a phishing attempt.
How to avoid Phishing Scams?
There are a few ways to stay safe from any email phishing attempt. Some best practices call for more time and effort on your part, but the cost of falling victim to a phishing scam is much higher.
1. Find your own links.
Don’t click on web links received in emails. When we click on links sent to us, our path is determined by the sender. Instead, go to the official website of the organization via the browser and look for the same information there. If the email web link is legitimate, you can also finish the action from the website. This is a guaranteed way to determine legitimacy.
2. Personally verify the sender’s identity.
If you receive a random email from a colleague or boss asking for urgent action, reach out to them personally (not by replying on the same email thread) to check if it was really them who sent the message.
3. Protect your accounts and passwords.
Use multi-factor authentication, unique passwords for all accounts, and a password manager to secure entry into your accounts. Also, always keep all your software updated to the latest versions.
4. Use managed email security.
Managed email security is a necessity for large organizations. A dynamic threat landscape demands that your security posture always be ahead of attackers. Managed email security adds a layer of defense to your organization with cutting-edge threat intelligence and detection techniques. Additionally, you get qualified IT experts who are available round-the-clock for instant threat response.
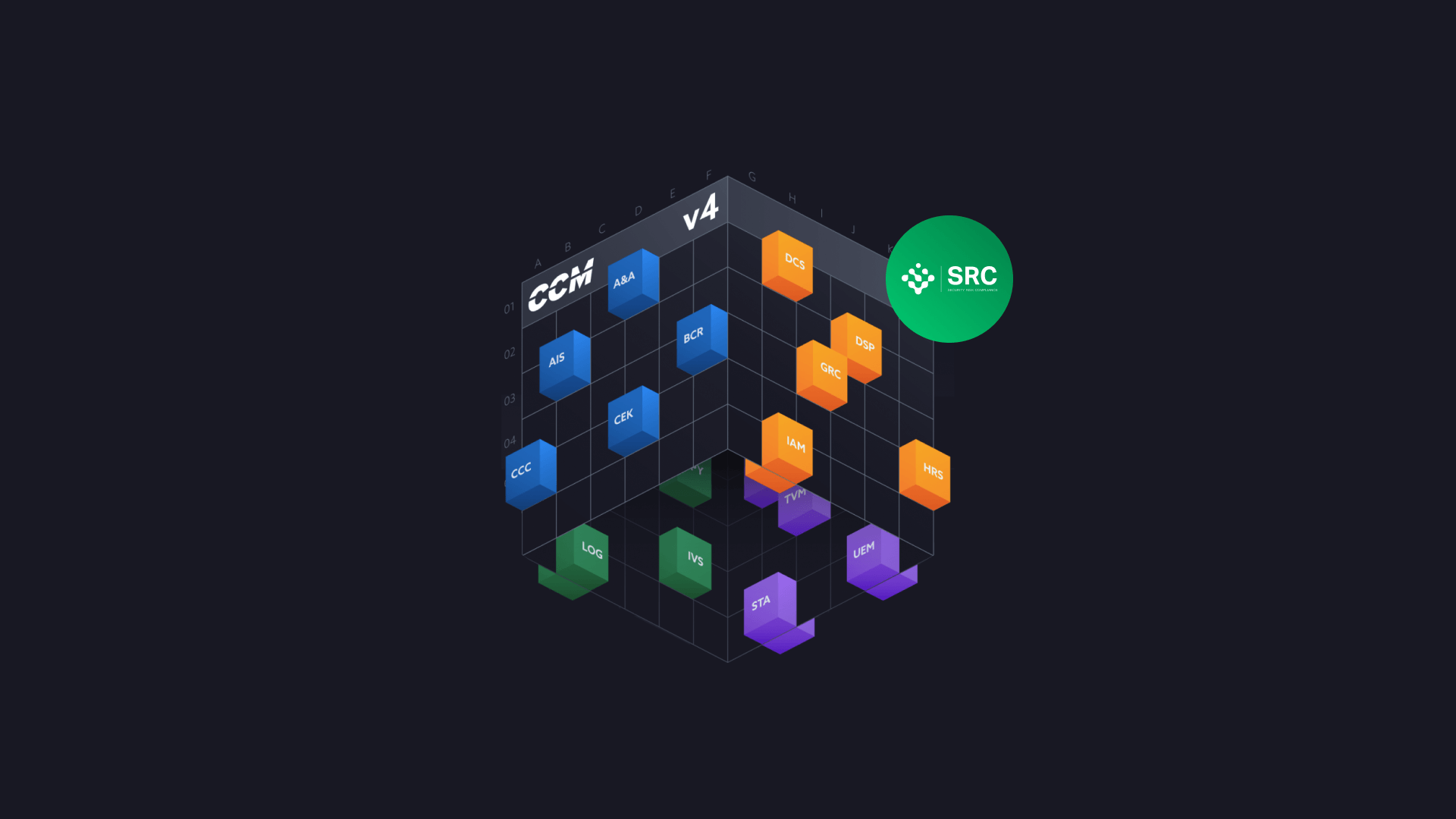
SRC security experts may support you in avoiding phishing scams by establishing the procedural and technical measures according to your reqirements. Check further details about our IT Security Consulting Services.