Startups are subject to cyber attacks - MiTM Case Study
A famous Berliner startup for supermarket delivery services heavily relies on IT solutions. After all, creating a comprehensive delivery system making use of customer interaction is technology-dependent. One thing they neglected in their development is data security.
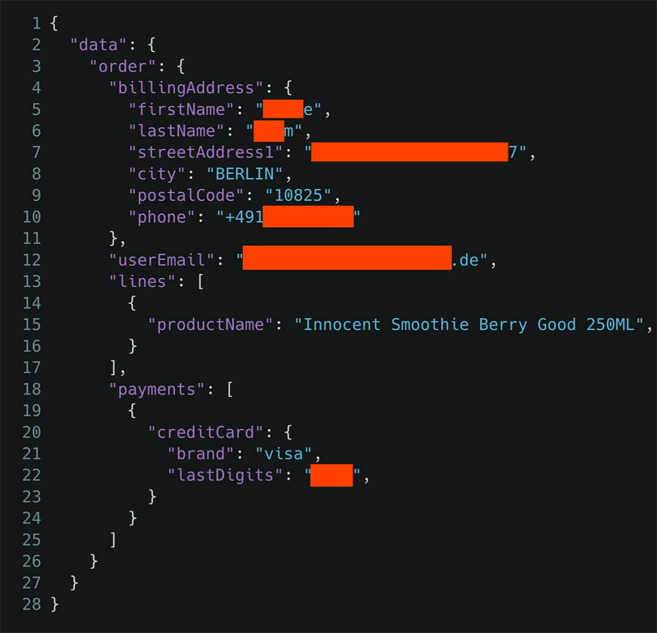
In March 2021, security researchers shared the result of an investigation aimed at pen-testing the startup company platform. They found a critical security gap that reveals the name, address, order, and even credit card details of thousands of customers. The security gap stems from the fact that the data interface was not properly secured allowing for access to customer information. As a rule of thumb: An advanced hacker could reveal the information of thousands of users by exploiting this gap in no more than half an hour.
The startup company and the pen-testing team did well by discovering this vulnerability before being exploited. This shows that investing in a secure system would protect against catastrophes.
What happened?
The researchers used a machine-in-the-middle proxy (MitM) to read the app's communications which represent the database queries. Using an authorization token stored in the app, they could connect directly to the startup company server and query the database.
Machine-in-the-middle (MITM) is a common type of cybersecurity attack that allows attackers to eavesdrop on the communication between two targets. The attack occurs between two legitimately communicating hosts, allowing the attacker to “listen” to a conversation they should typically not be able to listen to, hence the name “machine-in-the-middle.” MITM does not compromise only the confidentiality of the communication, but also it threatens the integrity since the attacker could have the necessary tool to manipulate the original communication.
The researchers took advantage of the following main flaws:
- Broken authentication and
- DB Injection.
It happens to be that these two flaws are number one and two on the top of the OWASP risks list for 2017.
Below image shows the returned JSON file of the experimental query passed to the database server taken from iphone-ticker.de:
Why had it happened?
Securing a cyber system stands for securing all system parts. We can see that the researchers exploited two vulnerabilities to extract the user's data:
- Authorization flaw: Their successful MiTM attack managed to intercept the communication between the client`s app and the server. They were able to view messages exchange including the critical ones. The success of the MiTM attack relies on improper authorization tokens set up and the lack of encryption when it is needed. For example, if the server/app messages were encrypted and the encryption key was stored safely and unlinked to the session token, researchers would not be able to act as the MiTM.
- Un-immune database: When the researchers managed to communicate to the server pretending to be the victim using their machine, they used a common database attack called “injection". It happens when an attacker injects an SQL query within a standard HTML text that is submitted to the server. The startup company server failed to recognize the submitted text as normal text and accordingly passed the SQL query to the database server which responded immediately with the query result (the company users' data in this case).
How to fix it!
In this startup case to avoid the authorization flaw, we see here that any system structure should always consider a proper token session time-out, also, linking any token to the original device MAC address is an essential matter to maintain identity assurance.
To immune their database, the startup company could counter the injection attack by disabling the special characters in any text submitted to the server like the HTML tagging characters “<>" and "</>".
Final remarks
We might agree that the adversaries in this particular case may not be interested in what their neighbors ordered for lunch or whether they received their order on time or not. However, the records revealed by the data leakage could be accessible by criminals of e-mail address/phone scammers who find themselves knowing someone's correct identification information like name and address. Also, some customer support agencies often ask for the last four digits of the bank account to confirm the caller's identity, consequently, we can see how easy it is for hackers to launch stalking attacks after obtaining this data.
According to the GDPR, every company is responsible for protecting the customers' data (whether data is stored or processed). Accordingly, reaching that security gap by a hacker before the pen-testing team would result in severe legal consequences for the startup company, in addition to extreme damage to the company's business reputation.
The startup company reacted quickly and secured this gap. Also, it stated that it took additional measures to protect the system in a step to show that their company learns from its mistakes and will more invest in securing its cyber system.